Cybersecurity has ceased to be a purely technical matter and has become a top-tier strategic element. In a context marked by automation, hyperconnectivity, and intensive data use, anticipating cybersecurity trends for 2026, it is no longer an option but an absolute necessity for companies, institutions, and public administrations.
Investing in security today means protecting business continuity tomorrow, preserving the trust of customers and partners, and complying with an increasingly demanding regulatory framework.
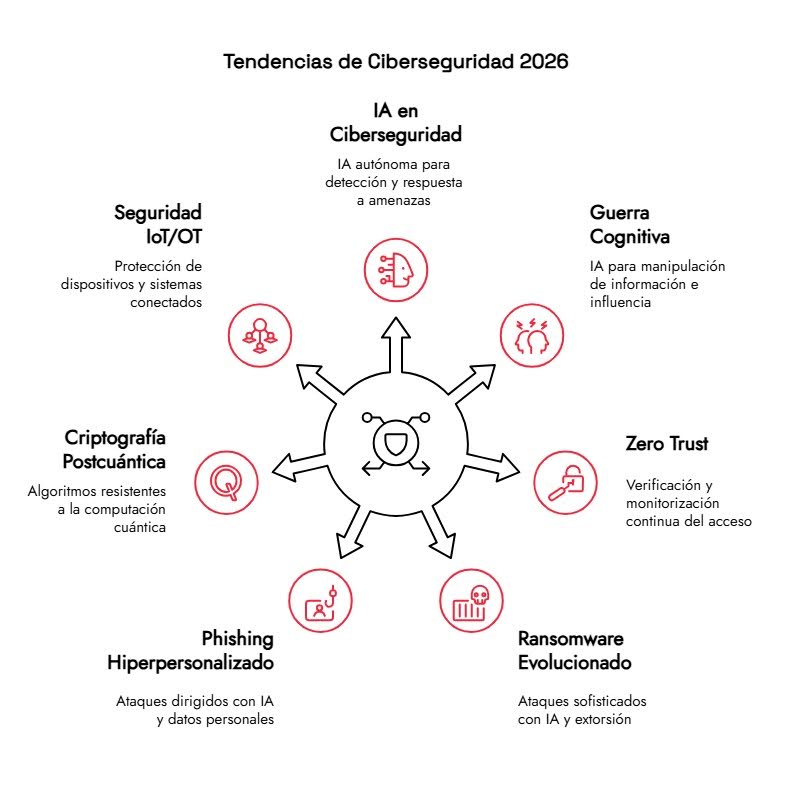
Next, we analyze the cybersecurity trends for 2026 that are already redefining how digital defense and risk management are understood.
Importance of cybersecurity in the current context
The digital environment in which organizations operate is more complex and exposed than ever before. Cloud migration, hybrid work, interconnected systems, and reliance on third parties have significantly expanded the attack surface.
Cybersecurity is no longer just about preventing external intrusions. Today it involves guaranteeing the confidentiality, integrity, and availability of information, protecting the digital supply chain, and having the capacity for early detection and response to incidents.
Furthermore, data protection and operational resilience regulations require organizations to adopt robust technical and organizational measures. Non-compliance not only incurs financial penalties but also directly impacts reputation and market trust.
In this scenario, staying up to date on cybersecurity trends is key to developing realistic, persistent strategies that adapt to increasingly sophisticated threats.
Discover the top cybersecurity trends for 2026
Technological evolution is progressing at the same pace as cyberattacks. Understanding where both are headed allows us to design more effective and sustainable defenses. These are the trends that will shape the short and medium term.
1. Artificial Intelligence and autonomous systems in cybersecurity
Artificial intelligence is no longer just a support tool, but a core component of security strategies. By 2026, the focus will shift to increasingly autonomous AI capable of analyzing complex contexts, correlating events, and making decisions without constant human intervention.
These technologies enable the detection of anomalous patterns in large volumes of data, anticipate malicious behavior, and reduce incident response times. Their value lies primarily in their ability to learn from previous attacks and adapt to new tactics.
However, this advance also poses risks. Attackers are using AI to automate campaigns and personalize attacks. It i,s and makes its detection more difficult. Therefore, defensive evolution must always be one step ahead.
Key areas of application of AI in cybersecurity
Among the most relevant uses are:
- Advanced phishing detection, analyzing emails, domains, social networks, the deep web, and the dark web.
- Reduction of false positives, a significant historical problem in security tools.
- Continuous monitoring of the digital footprint of organizations and their suppliers.
Solutions such as Kartos by Enthec integrate their own artificial intelligence to provide a precise, actionable view of risk, eliminating unnecessary noise and enabling informed decision-making.
2. Use of AI in Cognitive Warfare
Cognitive warfare represents one of the most sophisticated and worrying threats in the cybersecurity landscape for 2026. It involves operations designed to influence the perceptions, emotions, and behaviors of individuals and societies by manipulating information and leveraging generative artificial intelligence.
AI can analyze sentiment and emotions in real time, identify cognitive biases, and create personalized narratives for specific audiences. Furthermore, it enables the complete automation of disinformation campaigns, from generating content, distributing it, and measuring its impact in real time.
3. Zero Trust as a consolidated security model
The Zero Trust approach is no longer an emerging trend; it will consolidate as a benchmark standard in cybersecurity in 2026.
Its principle is clear: do not trust any user, device, or system by default.Regardless of whether it is inside or outside the corporate network, every access must be verified, authorized, and monitored.
This model is especially relevant in distributed environments with remote employees, cloud infrastructure, and multiple digital identities. Furthermore, microsegmentation limits lateral movement by potential attackers, thereby reducing the impact of a breach.
Adopting Zero Trust requires technical and cultural changes, but it offers a more realistic framework for addressing current threats.
4. Evolved ransomware: new models and persistent threats
The ransomware attacks remain at the forefront of global cyber threats and are far from stagnant; they continue to evolve. Throughout 2025, criminal organizations operating under the Ransomware-as-a-Service (RaaS) model maintained a consistent level of activity, demonstrating that this criminal scheme continues to generate profits and adapt to the environment.
Artificial intelligence has been integrated into all phases of the attack cycle, not just the development of malicious code. It encompasses everything from creating variants with greater obfuscation and evasion capabilities, to refining techniques for lateral movement within networks, to more sophisticated extortion methods that incorporate automated negotiations and psychological pressure tactics based on artificially generated content.
Looking ahead to 2026, the main concerns include:
- Multi-stage extortion: gradual leaking of information, direct pressure on customers and suppliers, and intimidation through AI-created synthetic material.
- Atomization of the criminal landscape, where small cells leverage AI tools to expand the reach of their operations.
- Faster incidents that are difficult to attribute. This complicates both the immediate response and subsequent investigations.
- Expansion of AI utilities for malicious purposes, specifically designed to automate and scale cyberattacks.
Given this scenario, organizations must review and update their backup strategies, recovery plans, and business continuity protocols. The 3-2-1 model (three copies of the information, stored on two different media, with at least one located off-site) remains a fundamental reference, complemented by regular restoration drills.
5. Hyper-personalized phishing and social engineering attacks
Phishing remains one of the most effective attack vectors and, far from disappearing, is evolving. In 2026, we are talking about
highly personalized phishing, driven by AI and by massive access to public information and previous leaks.
Attacks are no longer based on generic messages but on credible communications tailored to the recipient’s context and difficult to distinguish from legitimate interactions.
To address this cybersecurity trend, organizations must combine:
- Ongoing employee training.
- Behavior-based detection technologies.
- Multi-factor authentication and access control.
Cyber intelligence platforms allow the identification of active campaigns before they impact end users.
6. Quantum computing and post-quantum cryptography
ComputingAntiquity is progressing gradually, but its implications are already present in cybersecurity trends for 2026. Its ability to solve some mathematical issues puts traditional cryptographic systems at risk.
According to the National Institute of Standards and Technology (NIST), the transition to post-quantum cryptography must be initiated in advance to avoid future vulnerabilities.
Although it is not yet an immediate threat, organizations should assess their critical assets, identify vulnerable algorithms, and plan an orderly migration to standards resistant to quantum attacks.
7. Security in IoT and OT environments
The expansion of the Internet of Things (IoT) and connected industrial (OT) systems introduces new risks. Many devices have inherent safety limitations by design and operate in critical environments.
Protecting these ecosystems requires a specific approach that combines:
- Network segmentation.
- Continuous monitoring.
- Periodic firmware updates.
- Constant evaluation of exposed vulnerabilities.
IoT cybersecurity will remain one of the most significant trends in 2026, with a substantial impact across the industrial, energy, and healthcare sectors.
Discover our cybersecurity solution for businesses.
In this scenario, having accurate and up-to-date information is essential. At Kartos, we help organizations anticipate real threats through continuous monitoring, real-time alerts, and advanced risk analysis.
Thanks to its proprietary AI, Kartos provides a clear view of the company’s digital exposure and value chain, eliminating false positives and enabling action prioritization.
Such Artificial Intelligence has evolved that enables Kartos to be the only cybersecurity solution for businesses, capable of avoiding false positives in search results, thereby ensuring effective protection.
If you want to prepare your organization for 2026 cybersecurity trends, contact our team to learn how Kartos can help you strengthen your cybersecurity strategy starting today.