Our mobile phone is more than just a device: it’s the center of our digital lives. We use it to access our social media, online banking, medical services, and work communications.
But have you ever thought about what would happen if someone hijacked your phone number? This is precisely what happens with SIM swapping, an impersonation technique that is on the rise.
Before going into details, it’s worth presenting a solution that can be very useful for detecting an attack in time. Qondar, our tool, is a platform for individual cyber-surveillance to anticipate digital threats.
Qondar is an early warning system that identifies potential exposure of your personal information online and can help you detect signs of SIM swapping before it’s too late.
What is SIM swapping?
You may have read about it in recent news or heard it called SIM swap or SIM swapping, but what exactly is SIM swapping?It is a digital scam that involves duplicating your SIM card without your consent.
In other words, a cybercriminal can take over your phone line, redirecting your calls, messages, and, most worryingly, the verification codes that many services send via SMS.
The objective is clear: access your accounts using popular two-step verification (2FA) systems. Many banks, social media platforms, and email services use this method to verify your identity, but if the attacker already has your phone number, they can receive these codes and access your data as if they were you.
SIM swap: how does it work?
The technique is not new, but it has gained popularity in recent years. The modus operandi usually follows this scheme:
- Obtaining personal data. Through leaks, social engineering, or even social networks, the criminal collects enough information about you (name, ID, address, phone number, etc.).
- Impersonation. With this information, they contact your phone provider, posing as you, and request a duplicate SIM card, claiming the device has been lost or damaged.
- Activating the new SIM. Once the operator validates the request, the new SIM is activated, and your line will no longer be available on your device.
- Account access: The attacker tries to access your accounts. If you have SMS authentication enabled, he is already on the hook.
In minutes, someone can gain complete control over your personal data, networks, online banking, and more.
How can you tell if someone has swapped your SIM card?
Detecting an attack in time can mean avoiding serious losses or blocking access before it causes damage. Here are the clearest warning signs:
- Your mobile phone suddenly loses coverage in an area where you normally have a signal. You’re not receiving calls or messages, but there’s no apparent technical cause.
- You receive notifications of changes to your account (changed passwords, login attempts) in services you haven’t touched.
- There are unrecognized bank transactions or transfer attempts on your account.
- You receive an SMS or call from your operator confirming a SIM change that you did not request.
- You cannot access your email, social media, or online banking with your usual credentials.
If you experience any of these signs, act immediately. Call your operator to block the duplicate, contact your bank, and change the passwords for your main accounts from a secure device.
A tool like Qondar, our individual cyber-surveillance solution, can alert you to signs prior to an attack, such as the appearance of your data in security breaches or on dark web forums, allowing you to react before the SIM swap materializes.
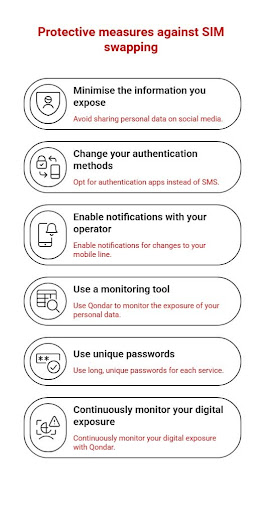
How to protect yourself from SIM swapping?
It is normal to wonder how to avoid SIM swapping or what we can do to protect ourselves from this dangerous technique. Here are some recommended measures:
1. Minimize the information exposed on networks
Avoid sharing information such as your phone number, date of birth, or address on social media. Even seemingly harmless information can be used to create a fake profile and impersonate you.
2. Change authentication methods
Whenever possible, avoid SMS authentication. Opt for authentication apps like Google Authenticator, Authy, or physical keys (like YubiKey), independent of your mobile phone line.
3. Activate notifications on your operator
Some carriers allow you to notify them of any line changes, such as SIM card duplication or portability requests. Activate these notifications if available.
4. Use unique passwords and a password manager.
If an attacker can’t guess or recover your password, it will be much harder for them to access your accounts, even with just your phone number. Use long, unique passwords for each service, and manage them with a secure password manager.
5. Continuously monitor your digital exposure with Qondar
Qondar, Enthec’s solution for individual users, continuously monitors whether your personal data has appeared in security breaches, on the dark web, in cybercriminal forums, or in any space where it could be used to prepare a SIM-swapping attack.
Thanks to its CTEM (Continuous Threat Exposure Management)- based model, Qondar does not perform a one-off analysis of your situation; it continuously evaluates your digital risk and sends you personalized alerts when it detects signs of danger.
SIM swapping: How to prevent it with an early warning tool
Attacks don’t always come in visible form. Often, personal data leaks online before a SIM swap. Emails, passwords, phone numbers, or addresses leaked in stolen databases are the cybercriminal’s first step.
Qondar lets you know if your data has appeared in a security breach, if someone is trying to steal your identity, or if your phone number has been compromised. This information is vital so you can take timely measures, such as changing your password, contacting your carrier, or even temporarily blocking certain services.
Thanks to its model-based approach, CTEM (Continuous Threat Exposure Management), Qondar doesn’t just analyze a snapshot of your digital situation; it continuously assesses your risks and adapts to the changing cybersecurity environment.
Why is SIM swapping an increasing threat in 2026?
SIM swapping is not an isolated problem. According to data from Europol and the National Cryptologic Center, these types of scams are rising in Europe. Attackers are targeting prominent public figures as well as ordinary citizens whose data has been exposed online.
SIM swapping is neither an isolated nor a new problem, but its reach has continued to grow. Several factors explain this increase:
- Greater digitization of critical services: Banking, insurance, healthcare, and public administration use the telephone as a verification tool, increasing the value of the phone number for attackers.
- Proliferation of data leaks. Every security breach that exposes millions of records provides criminals with the material they need to prepare social engineering attacks.
- Increasingly sophisticated techniques. Attackers use AI to generate convincing conversations with operators, mimic voices, or create fake documentation.
- Low barriers to entry. There are kits and tutorials on the dark web that make it easier for actors with little technical experience to carry out this attack.
The consequences of being a victim of a SIM swapping scam can include unauthorized bank transfers, identity theft to commit crimes, blocking of personal and professional accounts, loss of access to medical services or insurance in your name, and irreversible loss of digital assets such as cryptocurrencies.
Therefore, having tools that perform this monitoring automatically and constantly has become a real necessity.
What to do if you have already been a victim of SIM swapping?
If you believe you have suffered a SIM swap attack, act quickly by following these steps:
- Call your operator immediately. Report what happened and request that they block the fraudulent duplicate and restore control of your line.
- Contact your bank. Report the situation so they can block potential transfers and review your recent account activity.
- Change passwords from a secure device. Prioritize email, online banking, and social media. Use a trusted Wi-Fi network, never a public one.
- File a complaint. Contact the State security forces (National Police or Civil Guard) and INCIBE (017, the cybersecurity helpline).
- Review and strengthen your digital security. Remove SMS 2FA from all possible services and activate more secure authentication methods.
What can you do today?
Now that you know what SIM swap is and how easy it is to fall victim to this scam, you can make more informed decisions to protect yourself.
We recommend:
- Review your authentication methods in the most important digital services.
- Avoid using the phone number as the only verification method.
- Try Qondar, our cyber surveillance platform for individuals, which helps you keep your data safe with personalized alerts.
SIM swapping is a real, silent, and dangerous threat. You don’t have to be a celebrity to be targeted: all it takes is for your data to have been leaked, even if it’s on a website you registered with years ago.
Protecting yourself requires a combination of prevention, good digital practices, and tools that work for you.
Qondar by Enthec is precisely that: a digital shield that alerts you when something is wrong, when your data appears where it shouldn’t. Thanks to its continuous monitoring capacity and threat exposure management, it becomes a key ally in preventing SIM swapping before it happens.
Want to check if your information has already been exposed?
Get access to Qondar and take the first step to protecting your digital identity. Visit Enthec and protect your data before it’s too late.