Solutions
Extended Threat Intelligence
An army of XTI Watchbots to protect all sectors.
Challenges.
External Threat Intelligence
- Red
- DNS Health/Phishing
- Patch Management
- IP Reputation
- Web Security
- Document Leaks
- Credential leak
- Social networks
- Email security
- Third Party Risk
- Supplier Evaluation
- Cybersecurity in social networks
- Detection of leaked and exposed information
- Detection of information leak points
- FIND AND PROTECT YOUR VULNERABLE POINTS
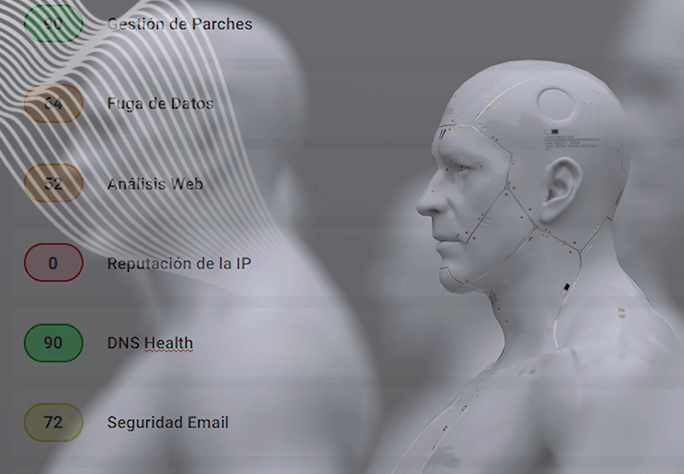
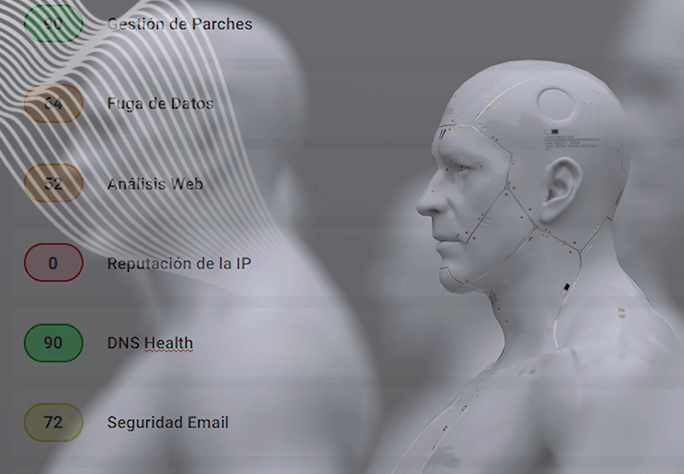
Riesgo de Terceros
Los ataques a empresas a través de sus proveedores o terceros colaboradores crecen cada año llegando a ser más del 80% de la causa durante el último año. Gracias a los XTI Watchbots de Kartos podrás asegurar tu compañía contra este problema, conociendo en tiempo real el estado de seguridad de sus proveedores, además del suyo propio.
Third-party risk
Third Party Risk
Attacks on companies through their suppliers or third-party collaborators grow every year, accounting for more than 80% of the cause during the last year. Thanks to the XTI Watchbots from Kartos you will be able to secure your company against this problem, knowing in real time the security status of your suppliers, in addition to your own.
Supplier Evaluation
Supplier Evaluation
Evaluation of the level of cybersecurity of suppliers before beginning the commercial relationship and for as long as it lasts. Automated and real-time detection of vulnerabilities associated with suppliers.
Cybersecurity in social networks
Cybersecurity in social networks
Unique approach in the market that allows the detection of conversations on networks related to hacktivism, fraud, phishing or fake news campaigns, among others, and conversations that may raise suspicion of an attack in preparation.
Detection of leaked and exposed information
Detection of leaked and exposed information
Location of all information leaked and exposed on the network about the organization that is available to anyone who knows how to look for it or has an interest in acquiring it to use it for their own benefit or to prepare an attack.
Detection of information leak points
Detection of information leak points
Locating the security gaps that cause these information leaks so that the entity can take actions that allow it to improve its defense systems and protect itself from possible attacks.
FIND AND PROTECT YOUR VULNERABLE POINTS
Supplier Evaluation
Evaluation of the level of cybersecurity of suppliers before beginning the commercial relationship and for as long as it lasts. Automated and real-time detection of vulnerabilities associated with suppliers.


Cybersecurity for the following sectors
Health
Recovery of leaked medical records. Detection of compromised passwords. Protection of the query and operations system. Protection of the hospital care system. Detection of security breaches. Evaluation of partners and suppliers. GDPR compliance.
Pharma
Insurance companies
Utilities
Education
Finance
Telecommunications
Industry
Public sector
Retail
Health
Recovery of leaked medical records. Detection of compromised passwords. Protection of the query and operations system. Protection of the hospital care system. Detection of security breaches. Evaluation of partners and suppliers. GDPR compliance.
Education
Public sector
Pharma
Finance
Retail
Insurance companies
Telecommunications
Utilities
Industry
Health
Recovery of leaked medical records. Detection of compromised passwords. Protection of the query and operations system. Protection of the hospital care system. Detection of security breaches. Evaluation of partners and suppliers. GDPR compliance.
Pharma
Insurance companies
Utilities
Education
Finance
Telecommunications
Industry
Public sector
Retail
Corporate areas
Management
Kartos protects business continuity, intellectual and industrial property, detects leaked corporate information and security breaches and increases the effectiveness of corporate cyber protection strategies without requiring a high cost of investment, implementation, personnel or maintenance. Provides two levels of reports adapted to the different profiles of the organization.
Security
Kartos provides the information necessary to control corporate information leaked and available on the Web, the Deep Web and the Dark Web, detect latent vulnerabilities, discover security gaps in the organization and flaws in the cyber protection strategy. Kartos works 24×7 in a non-intrusive manner and allows the level of corporate cybersecurity to be evaluated from the point of view of its effectiveness and cybersecurity culture.
IT
Kartos protects the operation and continuity of the organization’s systems by detecting latent vulnerabilities beyond the corporate perimeter and nullifying their effectiveness in a cyber attack. Kartos extends the corporate cybersecurity strategy through a solution that works 24×7 in a non-intrusive manner and its implementation, adoption and management are within the reach of any member of the organization.
Marketing
Kartos helps protect the brand by detecting latent vulnerabilities that can be used in a cyber attack to cause a reputation crisis. In addition, it prevents the usurpation of the brand identity for fraudulent purposes and protects customers and their data. Kartos allows the configuration of real-time alarms that are customizable by fields of interest to the marketing team.
Legal
Kartos helps with compliance with data protection regulations. Detects in real time the availability on the Web, the Dark Web and the Deep Web of sensitive corporate data protected by law. Through its real-time alarm configuration system that is customizable by field, the organization’s legal team will have the necessary information to detect data leaks and avoid the legal consequences of failures in its custody.
Detection of Compromised Elements
- Passwords and credentials
- Documents
- Web
- Information – Ransomware