To protect a technological infrastructure, one of the first measures implemented is hardening. The concept is simple: minimize a system’s attack surface by eliminating everything unnecessary, and reinforcing what remains.
Hardening a system is like removing all flammable material before someone tries to set it on fire. Services disabled, ports closed, default settings replaced, permissions reviewed.
Hardening networks and systems is now a fundamental practice in any cybersecurity strategy. Any organization that manages data, provides digital services, or relies on a connected infrastructure needs to implement it.
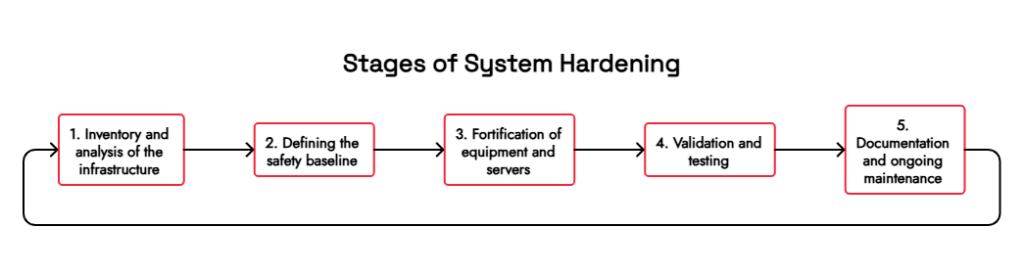
Phases of system hardening
The hardening process is not a one-time action. It is a structured cycle that should be thoroughly understood before implementation.
1. Inventory and analysis of the infrastructure
Before hardening anything, you have to know what exists. This phase includes identifying all assets (servers, network devices, and user equipment) and documenting their current configurations. Without a clear inventory, hardening is, by definition, incomplete.
2. Definition of the security baseline
Once the infrastructure is known, a minimum secure configuration for each system type can be defined.. There are widely used frameworks for this, such as the CIS Benchmarks (published by the
Center for Internet Security) or the NIST guides, which offer recommended configurations for the most common operating systems and applications.
3. Hardening of equipment and servers
This is where the technical work is carried out. The Equipment hardening encompasses actions such as:
- Uninstall unnecessary software.
- Disable unused services and ports.
- Apply the principle of least privilege to accounts and permissions.
- Change default credentials.
- Configure password and authentication policies.
Server hardening adds specific layers, such as secure configurations for web services, databases, remote access protocols, and event logging systems. A misconfigured server is, statistically, one of the most exploited entry points.
4. Validation and testing
Once the changes have been implemented, it is essential to verify that the system continues to function correctly and that the implemented measures are effective. . This includes functionality testing and vulnerability scans to confirm that no known vulnerabilities remain.
5. Documentation and ongoing maintenance
Hardening networks and systems doesn’t end with validation. Every software update, every new service added, or every infrastructure change can introduce new vulnerabilities. Documenting the process and conducting regular reviews are part of the cycle.
The hardening has limits: the exposed attack surface
Fortifying is necessary, but not sufficient. And this distinction is important.
The hardened system operates on what is under the organization’s direct control: its servers, its networks, its equipment. However,
a company’s actual attack surface extends far beyond its internal perimeter.
Data leaked on the dark web, compromised credentials circulating on underground forums, third-party services with vulnerabilities, similar domains used for impersonation… All of that is part of the threat landscape that any organization faces, and hardened security does not cover it.
This is where the continuous monitoring of the attack surface becomes an essential complement.
Why combine fortification with cyber surveillance
A fortified system without continuous monitoring is like a safe without an alarm; it is well protected, but no one is warned if someone tries to force it open from the outside.
The combination of bastioning with Continuous Management of Threat Exposure allows organizations not only to reduce their internal exposure, but also to detect in real time what information or assets are being exposed abroad.
KartosEnthec’s enterprise-oriented cyber surveillance solution, operates precisely at this layer. It continuously monitors the organization’s external attack surface, including leaked credentials, exposed assets, vulnerabilities, mentions in intelligence sources, and any other signals that might foreshadow an attack. It does not replace the hardening; it complements it by covering what the hardening, by its nature, cannot see.
This combined approach of hardening and continuous external monitoring best aligns with modern risk management frameworks and is being adopted by more organizations as attackers refine their methods.
A mature approach to a changing environment
Cybersecurity is not a state to be achieved; it is a process to be maintained. Hardening is a central part of that process, but it needs to be integrated into a broader strategy that also accounts for what happens outside the perimeter.
Threats evolve, environments change, and assets multiply.. Relying solely on internal hardening measures without visibility into external exposure leaves blind spots that attackers can exploit.
If your organization wants to build a solid security posture adapted to the current reality, the starting point is to know what it is exposed to, both internally and externally.
Do you want to know what information about your organization is currently exposed? Contact us for a first look at your external attack surface, with no commitment.