Passive cybersecurity attacks: Keys to identifying these types of invisible threats
When discussing cybersecurity, we often imagine exaggerated and obvious attacks: viruses that lock…
How to erase or reduce your digital footprint and minimize the risk of cyberattacks
Our online presence is broader than we imagine. Every search we make, every post we share, and…
Whaling: the attack that targets senior executives and keys to avoid it
Although we don't always consider it, cybercriminals often look for the most influential people…
Real-time vulnerability management: a step forward in cybersecurity
Vulnerability management has become one of the most critical elements within modern cybersecurity.…
Public image on the internet: how to Protect it from Digital Risks
We live in a digital age where our online presence is just as significant as our image in the real…
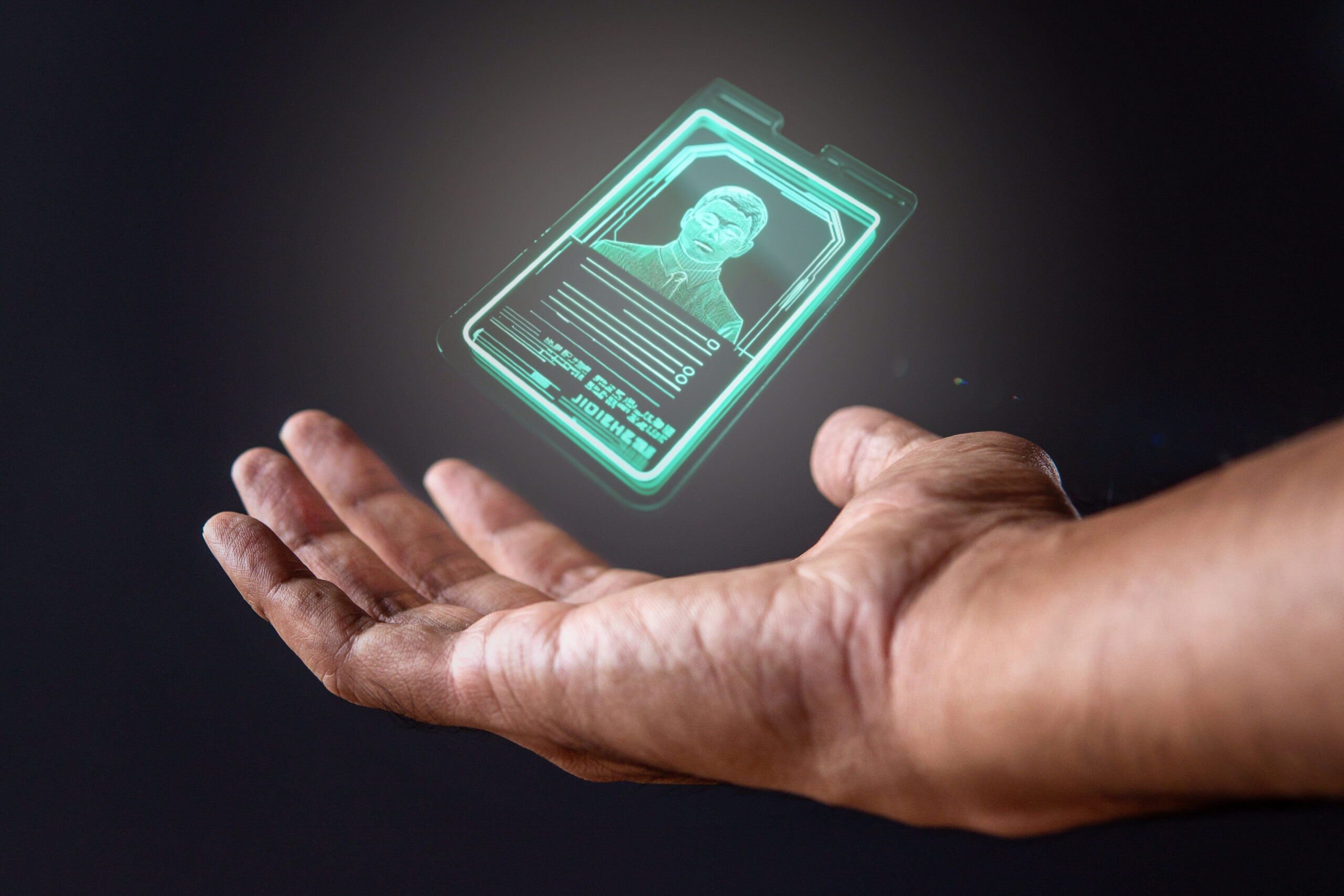
How to protect your digital identity against major threats
Protecting our digital identity has become a priority. Our data is constantly exposed to risks from…
Social engineering attacks on senior executives
Senior executives are desirable targets for social engineering attacks because they can access…
Deepfakes: what they are and how to detect them
In the digital information age, artificial intelligence (AI) has enabled surprising manipulation of…
How can your credit card data be stolen?
With the proliferation of online commerce, credit card data theft has become a common crime.…