Differences between IDS and IPS, and how they complement your security strategy
Most organizations invest in firewalls, antivirus software, and authentication systems, yet still experience incidents. The reason is usually the same: detecting a threat is not the same as stopping it, and stopping it without understanding what's happening creates blind spots. That's where IDS and IPS systems become essential.
This article explains what they are, how they differ, and, above all, how they fit into a security strategy that aims to go beyond reaction.
What is an IDS or an IPS, and what is it used for?
Before discussing differences, it's important to be clear about what we're talking about.
IDS: Detect to understand
An IDS (Intrusion Detection System)
monitors network traffic or system activity for suspicious behavior or known attack patterns. When it detects something out of the ordinary, it generates an alert.
What an IDS doesn't do is act.. It observes, records, and alerts, but it doesn't block. This might seem like a limitation, but it makes sense: the IDS is designed to give you visibility, not to interfere with legitimate traffic.
IPS: detect to block
An IPS (Intrusion Prevention System) goes one step further.. It works similarly to an IDS, analyzing traffic and detecting threats, but it can also act automatically by blocking a connection, discarding malicious packets, or isolating a network segment before an attack materializes.
The essential difference, therefore, is the capacity for response. While the IDS reports, the IPS intervenes.
IDS vs IPS: What are the real differences?
When discussing IDS vs IPS, the comparison is often limited to "one detects and the other blocks." But the difference is more nuanced.
Network position
The IDS is typically placed outside the main traffic flow, in passive mode. It receives a copy of the traffic (via a mirrored port, for example) and analyzes it without interfering. This makes it ideal for environments where availability is critical, and a false positive that could disrupt a legitimate connection cannot be risked.
The IPS, on the other hand, is located on the path of actual traffic.. Everything that enters or leaves passes through it. This allows it to operate in real time, but it also means that a failure or misconfiguration can degrade performance or block legitimate traffic.
False positives: the Achilles' heel of the IPS
This is a point that deserves attention. When an IPS blocks something incorrectly, that is, generates a false positive,the consequences can be immediate, such as a transaction that isn't processed, a user who can't access the service, or a service that goes down. Therefore, the
quality of the signatures and the detection rules is fundamental.
A well-configured IPS can drastically reduce containment time, but only if pre-detection is reliable.
The difference between IDS and IPS is not one of hierarchy, but of function.
A common mistake is thinking that IPS is "better" than IDS because it does more things. But the difference between IDS and IPS doesn't mean that one replaces the other.
In many mature environments, both coexist: the IDS provides visibility and historical context, while IPS handles the automated response. . They are complementary, not competing, functions.
In fact, many manufacturers offer solutions that integrate both capabilities (the so-called IDS-IPS combined systems, or IDPS), allowing the organization to configure which actions are taken automatically and which require human validation.
What limitations do IDS-IPS systems have?
Although they are valuable tools, IDS-IPS systems have limitations that should be known.
Perimeter visibility, not comprehensive
Intrusion detection systems (IDS/IPS) analyze the traffic passing through them. If the attacker is already inside the network, if the threat arrives through a poorly managed encrypted channel, or if the entry vector is an employee with compromised credentials, these systems may detect nothing.
Dependence on well-known firms
Signature-based systems only recognize threats that have already been cataloged; zero-day threats, highly customized attacks, or living-off-the-land techniques (using legitimate system tools to attack) can go unnoticed.
Absence of external vision
Neither the IDS nor the IPS analyzes what happens outside your perimeter.Leaked credentials on cybercrime forums, exposed data in public repositories, mentions of your company on the dark web, or vulnerabilities in the digital supply chain. A different approach is needed for these.
How to complement IDS-IPS systems with a CTEM strategy
This is where many organizations make the leap to a more proactive model, such as CTEM (Continuous Threat Exposure Management).
The CTEM approach does not replace IDS-IPS systems but rather integrates them into a broader cycle: identify, prioritize, validate, mobilize, and remediate exposure to threats continuously, from both internal and external perspectives.
The external cyber-surveillance layer
While an IDS-IPS monitors what happens inside the perimeter, a cyber surveillance solution monitors what happens outside, that is, what information about your organization circulates on the surface, deep, and dark web; what digital assets are exposed without your knowledge; what vulnerabilities your attack surface has that are visible from the outside.
Kartos, Enthec's automated monitoring tool, is designed to address this layer precisely. It enables organizations to maintain continuous visibility into their external digital exposure, detect data leaks, identify compromised assets, and anticipate threats before they trigger IPS alerts.
It's not about adding another tool. It's about to close the blind spot that IDS-IPS systems, by their nature, cannot cover.
What should you consider when choosing or evaluating your IDS-IPS system?
If you're reviewing your security architecture, here are some criteria worth considering:
- Behavior-based detection capability not only in terms of signatures but also for addressing unknown threats.
- Integration with your SIEM or other event correlation tools, so that alerts have context.
- False positive management, especially if you opt for an IPS in active mode.
- Encrypted traffic coverage, since a growing portion of malicious traffic travels over HTTPS.
- Complementary visibility on the external attack surface, which IDS-IPS systems do not cover on their own.
The IDS-IPS systems are a relevant component in any serious security architecture. They enable detection of anomalous activity, response to known attacks, and maintenance of an event log that facilitates forensic investigations. But they are reactive in nature.
Modern cybersecurity demands going further: continuously monitoring external exposure, understanding how attackers perceive you before they act, and managing risks with a 360-degree view.
If you want to know how Kartos can complement your security infrastructure with continuous cyber surveillance focused on CTEM, discover what Enthec can do for your organization.
Do you have questions about how these solutions fit into your specific context? Contact the Enthec team and analyze your digital exposure without obligation.
Systems hardening: what it is, phases, and why it should be combined with attack surface surveillance
To protect a technological infrastructure, one of the first measures implemented is hardening. The concept is simple: minimize a system's attack surface by eliminating everything unnecessary, and reinforcing what remains.
Hardening a system is like removing all flammable material before someone tries to set it on fire. Services disabled, ports closed, default settings replaced, permissions reviewed.
Hardening networks and systems is now a fundamental practice in any cybersecurity strategy. Any organization that manages data, provides digital services, or relies on a connected infrastructure needs to implement it.
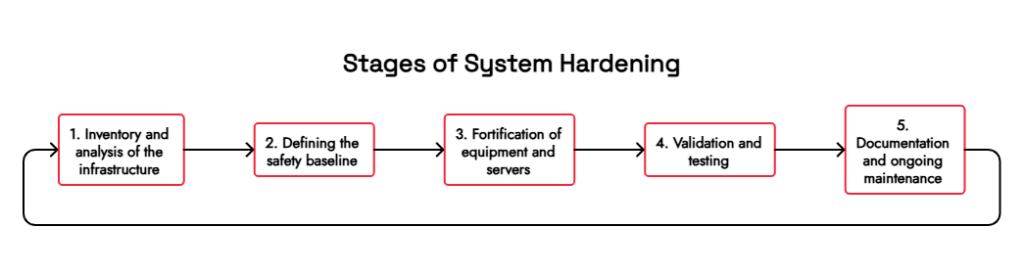
Phases of system hardening
The hardening process is not a one-time action. It is a structured cycle that should be thoroughly understood before implementation.
1. Inventory and analysis of the infrastructure
Before hardening anything, you have to know what exists. This phase includes identifying all assets (servers, network devices, and user equipment) and documenting their current configurations. Without a clear inventory, hardening is, by definition, incomplete.
2. Definition of the security baseline
Once the infrastructure is known, a minimum secure configuration for each system type can be defined.. There are widely used frameworks for this, such as the CIS Benchmarks (published by the
Center for Internet Security) or the NIST guides, which offer recommended configurations for the most common operating systems and applications.
3. Hardening of equipment and servers
This is where the technical work is carried out. The Equipment hardening encompasses actions such as:
- Uninstall unnecessary software.
- Disable unused services and ports.
- Apply the principle of least privilege to accounts and permissions.
- Change default credentials.
- Configure password and authentication policies.
Server hardening adds specific layers, such as secure configurations for web services, databases, remote access protocols, and event logging systems. A misconfigured server is, statistically, one of the most exploited entry points.
4. Validation and testing
Once the changes have been implemented, it is essential to verify that the system continues to function correctly and that the implemented measures are effective. . This includes functionality testing and vulnerability scans to confirm that no known vulnerabilities remain.
5. Documentation and ongoing maintenance
Hardening networks and systems doesn't end with validation. Every software update, every new service added, or every infrastructure change can introduce new vulnerabilities. Documenting the process and conducting regular reviews are part of the cycle.
The hardening has limits: the exposed attack surface
Fortifying is necessary, but not sufficient. And this distinction is important.
The hardened system operates on what is under the organization's direct control: its servers, its networks, its equipment. However,
a company's actual attack surface extends far beyond its internal perimeter.
Data leaked on the dark web, compromised credentials circulating on underground forums, third-party services with vulnerabilities, similar domains used for impersonation… All of that is part of the threat landscape that any organization faces, and hardened security does not cover it.
This is where the continuous monitoring of the attack surface becomes an essential complement.
Why combine fortification with cyber surveillance
A fortified system without continuous monitoring is like a safe without an alarm; it is well protected, but no one is warned if someone tries to force it open from the outside.
The combination of bastioning with Continuous Management of Threat Exposure allows organizations not only to reduce their internal exposure, but also to detect in real time what information or assets are being exposed abroad.
KartosEnthec's enterprise-oriented cyber surveillance solution, operates precisely at this layer. It continuously monitors the organization's external attack surface, including leaked credentials, exposed assets, vulnerabilities, mentions in intelligence sources, and any other signals that might foreshadow an attack. It does not replace the hardening; it complements it by covering what the hardening, by its nature, cannot see.
This combined approach of hardening and continuous external monitoring best aligns with modern risk management frameworks and is being adopted by more organizations as attackers refine their methods.
A mature approach to a changing environment
Cybersecurity is not a state to be achieved; it is a process to be maintained. Hardening is a central part of that process, but it needs to be integrated into a broader strategy that also accounts for what happens outside the perimeter.
Threats evolve, environments change, and assets multiply.. Relying solely on internal hardening measures without visibility into external exposure leaves blind spots that attackers can exploit.
If your organization wants to build a solid security posture adapted to the current reality, the starting point is to know what it is exposed to, both internally and externally.
Do you want to know what information about your organization is currently exposed? Contact us for a first look at your external attack surface, with no commitment.
Threat hunting: 3 reasons why it is necessary to have it
Threat hunting is a proactive cybersecurity practice that allows organizations to detect and neutralize advanced threats before they cause harm. In a context where attacks are becoming increasingly sophisticated and the average time an attacker spends within a network remains alarmingly high, relying solely on automated detection tools is no longer sufficient.
In this article, we explain what threat hunting is, how to implement it step by step, what you need to get started, and why it has become a pillar of modern corporate cybersecurity.
What is Threat hunting?
Threat hunting is a proactive process of searching for and detecting cyber threats capable of evading traditional security defences. Unlike reactive methods that rely on automated alerts, threat hunting involves actively searching for suspicious or malicious activity within the system or network, both internally and externally. The primary goal of threat hunting is to identify, mitigate, or nullify advanced threats before they can cause significant damage. This includes the detection of advanced persistent attacks (APTs), malware, exposed vulnerabilities and other risk factors that may not be detected by conventional security tools.
Threat hunting methodology
Now that you know exactly what Threat hunting is, it is essential that you discover its methodology. This process generally follows an iterative cycle that includes the following phases:
- Hypothesis. Threat hunting starts with formulating threat hypotheses based on threat intelligence, behavioral analysis, and knowledge of the environment.
- Data collection. Data is collected from a variety of sources, such as event logs, network monitoring, and endpoint data.
- Analysis. The collected data is analyzed for unusual patterns or indicators of compromise (IoCs).
- Research. If suspicious activity is identified, further investigation is carried out to determine the nature and extent of the threat.
- Response. If a threat is confirmed, measures are taken to contain, nullify, or mitigate the impact.
Threat hunting uses a variety of tools and techniques, including:
- Intrusion detection systems (IDS): to monitor and analyze network traffic for suspicious activity.
- Log and behavioral analysis: to review and correlate events recorded in different systems and identify deviations in the normal behavior of users and systems.
- Threat intelligence: to obtain information on open breaches and exposed vulnerabilities on the web, dark web, deep web, and social networks.
How to do Threat hunting: steps to follow
Implementing threat hunting effectively requires a structured process. These are the fundamental steps:
- Define objectives and strategy. Determine what you want to achieve, identify advanced threats or improve incident detection, and develop a strategy that includes the necessary resources, tools, and procedures.
- Form a Threat hunting team. The team must have experience in cybersecurity and data analysis, and it is essential that they stay up to date on the latest threats and techniques.
- Collect and analyze data. Compilation through event logs, network traffic, and Intrusion Detection Systems (IDS), automated Cyberintelligence. platforms.
- Formulate the hypotheses. Based on threat intelligence and behavioral analysis, hypotheses about potential threats are formulated, and steps are defined to investigate each.
- Execute the hunt. Active searches of collected data are conducted to identify suspicious activity. If indications of a threat are found, further investigation is conducted to confirm the nature and extent.
- Respond and mitigate. When a threat is confirmed, measures are taken to contain, nullify, or mitigate its impact.
- Documentation and reporting. All findings and actions taken are documented, and reports are provided to senior management and cybersecurity managers to improve defenses and security strategies.
What is needed to start threat hunting?
To implement an effective Threat Hunting program, we need to prepare and organize several key components to ensure its success. These fundamental elements include proper team selection, collection and analysis of relevant data, and integration of threat intelligence.
Human capital
Selecting the right threat hunting team is crucial to the success of the strategy. A threat hunting team should combine technical skills, practical experience, and the ability to work as a team. The threat hunting team should be composed of professionals with backgrounds in cybersecurity, data analysis, attacker techniques and procedures, with official certifications such as Certified Information Systems Security Professional (CISSP), Certified Ethical Hacker (CEH), or GIAC Certified Incident Handler (GCIH), and, if possible, extensive hands-on experience. The team must be able to work collaboratively and communicate their findings effectively to other departments and senior management. They should be continuously updated on cybersecurity and threats.
Data
To initiate threat hunting, it is essential to collect and analyze a variety of data that can indicate suspicious or malicious activity. This data should be extracted from event logs, such as system or security logs; network traffic, such as packet captures or network flows; endpoint data, such as activity logs or sensor data; threat intelligence, such as indicators of compromise or information gathered from monitoring external sources; user data, such as authentication logs or behavioural analysis; and data on exposed vulnerabilities and open breaches extracted from scans of the organisation's internal and external attack surfaces.
Threat Intelligence
Threat Intelligence focuses on the collection, analysis, and utilization of information about potential and current threats that may affect an organization's security. It provides detailed insight into malicious actors, their tactics, techniques, and procedures (TTPs), as well as exposed vulnerabilities and open security breaches that can be exploited to execute an attack. In threat hunting, threat intelligence serves as a solid foundation, guiding the team in identifying and mitigating risks. With access to up-to-date, accurate threat information, threat hunting professionals can anticipate and detect suspicious activity before it escalates into a security incident. In addition, Threat Intelligence enables prioritization of countermeasure efforts by focusing on the most relevant and immediate threats to the organization.
3 reasons why threat hunting is necessary in your organization
Threat hunting offers several key features and advantages that distinguish it from traditional security practices. The most relevant of these are highlighted below:
1. Proactive and immediate approach
Unlike traditional security methods that tend to be reactive, threat hunting empowers organizations to anticipate threats before they materialize. This proactive approach involves actively looking for signs of malicious activity rather than waiting for incidents to occur. By taking an immediate approach, threat hunting professionals can identify and neutralize threats in real time, minimizing the potential impact on the organization. This not only reduces incident response time but also improves the organization's ability to prevent future attacks. In addition, the proactive approach allows organizations to stay one step ahead of attackers by quickly adapting to new tactics and techniques used by malicious actors.
You may be interested in→ Proactive security: what is it and why use it to prevent and detect threats and cyberattacks?
2. Continuous improvement
Threat hunting enables organizations to constantly evolve and adapt to new threats and tactics employed by malicious actors. Through threat hunting, security teams can identify patterns and trends in threats, allowing them to continuously adjust and improve their defense strategies. Continuous improvement involves a constant feedback loop in which threat hunting findings are used to refine security policies, update detection tools and techniques, and train staff on new defense tactics. This process not only strengthens the organization's security posture but also increases resilience to future attacks.
3. High adaptability
Through threat hunting, organizations can quickly adjust their defense strategies in response to emerging threats and evolving attacker tactics. Adaptability in threat hunting involves continuously updating the tools, techniques, and procedures used to detect and mitigate threats. Thanks to this adaptability, security teams can respond more effectively to new challenges and vulnerabilities that emerge in the cybersecurity landscape. In addition, adaptability enables organizations to integrate new technologies and methodologies into their defense processes, thereby improving their ability to protect their critical assets.
Types of threat hunting according to need
Organizations can adopt different threat hunting models depending on their specific needs. Each approach offers a different perspective for identifying and mitigating threats.
Intelligence models
These models focus on identifying cyber threats using Cyber Threat Intelligence. They enable organizations to identify suspicious activities and patterns of behavior that could indicate the presence of malicious actors, as well as exposed vulnerabilities and open gaps in the network, using indicators of compromise obtained from threat intelligence sources. They address the organization's need to detect, monitor, and understand threats at its external perimeter to neutralize them or respond effectively to their use by cybercriminals.
Hypothesis models
These models focus on formulating hypotheses about potential cyber threats. They rely on the knowledge and experience of security analysts to develop plausible assumptions about potential attacks, how they could be executed, and the vulnerabilities that could be exploited. They respond to the organization's need to anticipate any threat and proactively adapt to new ones as they emerge.
Personal models
These are advanced models tailored to an organization's specific needs. They are based on in-depth knowledge of the corporate environment, weaknesses, and particular requirements, and use the organization's own data and patterns to identify potential threats. They respond to the need to detect specific threats, adapt the strategy to their infrastructure and operations, and optimize organizational resources. These models can be run through human teams, advanced Cyber Intelligence platforms that allow search customization, or a combination of both.
Discover how Kartos helps you with your threat hunting strategy
Kartos is the corporate cyber surveillance platform developed by Enthec, enabling you to implement and scale a threat-hunting strategy within your organization. Its continuous, automated, and customizable monitoring capabilities of the internet, the deep web, the dark web, and social networks keep you permanently informed about exposed vulnerabilities and open gaps that can become attack vectors.
Thanks to its proprietary AI, Kartos eliminates false positives in search results, ensuring that every piece of data it receives is truly useful for decision-making and neutralizing latent threats. Furthermore, it issues real-time alarms, it sends constantly updated information, and generates detailed reports on its findings.
Want to know how Kartos can strengthen your threat hunting program? Please contact our team to learn more about the full range of possibilities our corporate surveillance solutions offer.
The impact of man-in-the-middle attacks on companies
Communications security is a cornerstone of any man-in-the-middle cybersecurity strategy. Cybercriminals are constantly refining their techniques to intercept data and exploit vulnerabilities undetected. Among all the methods they employ, the Man-in-the-Middle (MitM) attack stands out for its ability to compromise highly sensitive information without any of the parties involved noticing.
But what exactly is a Man-in-the-Middle attack, and how can it affect a company? In this article, we explain its characteristics, impact, real-world examples, and how to protect yourself against this type of cyber threat.
Discover how advanced solutions like Kartos can help you protect your company's communications and prevent such attacks.
What is a Man-in-the-Middle attack?
A Man-in-the-Middle attack occurs when a cybercriminal is positioned between two parties who believe they are communicating directly with each other. The attacker intercepts the information, modifies it if desired, and forwards it without any party suspecting anything.
Imagine you're in a coffee shop, and you connect to public Wi-Fi to check your work email. Unknowingly, a hacker is on the same network and has created a fake access point with the same name as the premises' Wi-Fi. When you enter your login credentials, the attacker captures them without you noticing.
MitM attacks can occur in various contexts: open Wi-Fi networks, corporate email, HTTPS sessions with forged certificates, or even communications between a company's internal systems.
What dangers does a Man-in-the-Middle attack pose?
For businesses, a Man-in-the-Middle scam can have devastating consequences. Confidential information is put at risk, and relationships with customers and suppliers can also be affected. Let's look at some of the most significant impacts:
1. Credential theft and unauthorized access
Man-in-the-middle attacks can capture sensitive data such as usernames, passwords, and corporate service access credentials. A cybercriminal with access to this data could perform financial fraud, modify key information, or even sabotage internal processes.
2. Identity theft and financial fraud
Sometimes, the attacker intercepts the information and modifies it in real-time.
For example, a company may transfer money to a supplier. If a hacker has compromised the communication channel, he can alter the account number in the message before it reaches the recipient. Thus, the money ends up in the attacker's account instead of the provider's.
This attack is becoming more common in business transactions and electronic payments, and many businesses have lost large sums of money.
3. Leaking sensitive data
Man-in-the-middle attacks can also spy on a company's communications. If employees send unencrypted emails or use unprotected public Wi-Fi networks, an attacker can gather insights without anyone noticing.
This poses a significant risk for companies that handle sensitive data, such as law firms, technology companies, and financial institutions. Data breaches can damage a company's reputation and lead to legal penalties for non-compliance with data protection regulations.
4. Reputational damage and loss of trust from customers and partners
Businesses depend on the trust of their customers and business partners. If a company suffers a Man-in-the-Middle attack and customer data is compromised, its corporate image will be affected.
People are becoming increasingly aware of the importance of digital security, and such an incident can prompt customers and partners to seek safer alternatives.
5. Industrial espionage and intellectual property theft
Sectors such as legal, pharmaceutical, technology, and defense are priority targets. An attacker with continuous access to a company's communications can exfiltrate valuable intellectual property for weeks or months before being detected.
Real-world examples of Man-in-the-Middle attacks
To better understand the scope of these attacks, let's look at a real-world examples of a Man-in-the-Middle attack:
Attack on Wi-Fi networks in European airports (2015)
In 2015, security researchers discovered a large-scale Man-in-the-Middle (MitM) attack on public Wi-Fi networks in European airports. The cybercriminals had installed fake access points with names similar to those of legitimate networks.
When the passengers connected, the attackers could intercept login credentials, banking information, and personal data. Many business executives were victims without even realizing it.
This attack demonstrated how easy it is to exploit insecure connections and how a cybersecurity failure can jeopardize critical business data.
Operation Dark Caracal (2012–2017)
Researchers from the EFF and Lookout documented a massive espionage campaign attributed to a Lebanese state actor. The attackers deployed man-in-the-middle (MitM) infrastructure to intercept communications of journalists, lawyers, military personnel, and businesses in more than 21 countries, exfiltrating confidential documents, private conversations, and credentials over several years.
MitM attacks on online banking in Spain (recurring, 2020–2025)
INCIBE has documented multiple campaigns targeting corporate clients of Spanish banking entities, combining MitM attacks with phishing to capture access credentials to business online banking platforms and authorize fraudulent transfers.
The usual modus operandi follows a well-defined pattern. The attacker intercepts the active session between the employee and the bank portal, captures the OTP in real time, and immediately reuses it before it expires, thereby bypassing the Strong Customer Authentication (SCA) required by PSD2 regulations. The money appears to be transferred legitimately to accounts under the attacker's control, and the company only detects the fraud when it reviews its bank transactions.
How to protect your company from a Man in the Middle attack
Fortunately, there are several strategies to minimize the risk of a Man in the Middle attack. Here are some key measures:
1. Use of encryption in all communications
Data encryption is one of the best defenses against these attacks. HTTPS, VPNs, and encrypted emails should be used whenever sensitive information is exchanged.
2. Avoid public wifi networks
Open Wi-Fi networks pose a significant risk. If employees need to connect in a public place, they should use a VPN to protect their data traffic.
3. Implementing Multi-Factor Authentication (MFA)
If an attacker intercepts credentials, multi-factor authentication can prevent them from accessing the account. This method adds an extra layer of security, such as a code sent to the user's mobile.
4. Network traffic monitoring
Businesses should use security tools to detect suspicious activity on their network. Traffic analysis can identify unusual patterns that indicate the presence of an attacker.
5. Staff education and awareness
Many attacks exploit employees' lack of knowledge. Training staff in good digital security practices, such as recognizing fake websites and avoiding using unsecured networks, is essential.
6. Digital certificates and electronic signatures
Businesses can use digital certificates to authenticate their communications. This makes it difficult for attackers to impersonate identities or modify messages.
The Man-in-the-Middle attack is one of the most dangerous threats in enterprise cybersecurity. In minutes, it can compromise critical data, cause financial losses, and damage a company's reputation.
The Man-in-the-Middle attack, an active threat in 2026
As such, organizations must adopt protective measures, such as data encryption, multi-factor authentication, and staff awareness. Advanced cybersecurity solutions, such as Enthec's Kartos, can be essential for detecting and blocking MitM attacks in real time, ensuring the protection of your company's sensitive information.
In a world where digital security is more important than ever, being prepared can distinguish a safe company from another victim of cybercriminals.
Compliance with CRA regulation: How can you achieve it in your company?
The CRA or Cyber Resilience Act regulation marks a turning point in cybersecurity regulation in the European Union. This cyber resilience law establishes, for the first time, a uniform legal framework for the introduction of products with digital elements into the European market, from enterprise software and IoT devices to critical infrastructure components.
And the deadlines are closer than many companies realize. Vulnerability reporting obligations will apply starting on September 11, 2026, while the full implementation of the cyber resilience regulation will arrive on December 11, 2027. All operators involved in the value chain of products with digital elements must know and prepare to comply with their obligations before time runs out.
What does this mean in practice for your company? Who exactly is bound by the European cyber resilience law? And how can you structure compliance without it becoming an unmanageable burden for your teams?
This is where Kartos comes in, Enthec's cyber-surveillance platform based on a Continuous Threat Exposure Management model. Kartos allows you to proactively identify, monitor, and manage your organization's and your suppliers' external exposure, aligning directly with the requirements of the CRA regulation.
What is CRA regulation?
The CRA regulation, or cyber resilience regulation, is a legislative proposal of the European Union that seeks to ensure the safety of products with digital components throughout their life cycle.
This horizontal regulation affects all types of devices connected to the internet, from business management software to smart home appliances. The objective is clear: prevent security flaws from becoming entry points for attackers.
This cyber resilience law requires manufacturers, distributors, and importers to comply with a series of security requirements, including:
- Risk assessment before launching the product.
- Active vulnerability management.
- Transparency about security incidents.
- Security updates throughout the product's life.
According to a report from the European Union Agency for Cybersecurity (ENISA), over 50% of attacks in Europe originate from known vulnerabilities that remain unpatched.
Who is affected by the CRA regulation?
Although it may seem that only technology companies should be concerned, any organization that markets products with digital elements in the EU is subject to this regulation.
That includes:
- Software manufacturers.
- Companies that integrate digital systems.
- Connected hardware distributors.
- To a lesser extent, business users are obliged to demonstrate good practices in the digital supply chain.
In this sense, if your company integrates third-party software into its processes, you should check that these suppliers are aligned with the standards of the CRA regulation. If they fail, the problem can also reach your business. Under our third-party license, you will be able to manage these relevant issues.
You may be interested→ Keys to carrying out supplier evaluation: how to manage third parties in your company.
CRA regulation deadlines: what you need to know in 2026
The European cyber resilience law came into force on December 11, 2024. From then on, the phased implementation schedule is as follows:
- September of 2026: The obligations to report incidents and vulnerabilities to ENISA become applicable.
- December 2027: Full application of the regulation. All products with digital elements must comply with all applicable requirements to be marketed with a CE marking.
Companies that have not yet begun their adaptation process are, in practice, at significant regulatory risk.
How to achieve compliance with CRA regulations?
Compliance with CRA regulations is not a one-day task, but a continuous process that requires planning, resources, and strategic vision. Here are some keys to tackling it successfully:
1. Map your external attack surface
Before taking action, you need to know what's exposed. The CRA regulation requires manufacturers to understand and manage the risks associated with their products. The first step is to conduct a thorough inventory of digital assets, including domains, subdomains, IPs, exposed services, leaked credentials, and third-party dependencies.
With Kartos, you can get an up-to-date, automated view of your external exposure, without manual intervention or false positives.
2. Establish a vulnerability management process
The cyber resilience law requires manufacturers to identify, document, and correct vulnerabilities throughout the product's lifecycle. This implies having a formal vulnerability management process that includes prioritization by criticality and recording of actions taken.
3. Implement a CTEM strategy
One of the best ways to comply with CRA regulations is to adopt a Continuous Threat Exposure Management model(CTEM). This strategy is based on:
- Constantly identify new threats
- Validate the effectiveness of your security controls.
- Automate detection and response processes.
Through Kartos, we offer precisely a CTEM-based approach that perfectly fits this need.
4. Establish incident reporting processes
The cyber resilience regulation establishes strict notification obligations; actively exploited vulnerabilities and serious security incidents must be reported to ENISA within 24 hours of the manufacturer becoming aware of them.
Having the processes and tools in place to detect, classify, and report incidents on time is not optional; it is a legal requirement starting in December 2026.
5. Document and audit
The cyber resilience regulations require transparency. Therefore, it is essential to document security actions, to implement controls, and to record incidents. This way, if an audit occurs or a decision needs to be justified, you'll have all the necessary documentation.
Benefits of complying with the CRA regulation
Although it may seem like just another obligation, the truth is that compliance with the CRA regulation can become a competitive advantage:
- Improves your brand reputation.
- Increases the confidence of customers and partners.
- Reduces the risk of sanctions and economic losses.
- Prepares you for future similar regulatory frameworks.
Plus, keeping your digital exposure under control minimizes the risk of cyberattacks, which cause billions of euros in annual losses, according to data from Cybersecurity Ventures.
Kartos: your ally in compliance
You are not alone in this process. Enthec offers solutions designed to help you address all of these challenges. With Kartos, you can:
- Continuously detect external threats.
- Prioritize corrective actions.
- Comply with the requirements of the cyber resilience regulation more simply.
Adapting to the CRA regulation should not be seen as a burden but as an opportunity to improve your company's cybersecurity posture.. The sooner you start, the better prepared you will be to face the digital challenges that lie ahead.
At Enthec, we know security is not static. That's why we offer tools that evolve with your company.
Do you want to see how Kartos can help you comply with CRA regulations simply and effectively? Contact us to start working together.
Cyber-intelligence: what it is and what are its advantages of use at a strategic and tactical level
Cyberintelligence has become a strategic pillar of modern cybersecurity. In an environment where digital threats evolve at the same speed as the technology that fuels them, understanding what cyber intelligence is and how to apply it effectively becomes a determining factor for a proactive organization.
What is cyber intelligence?
Cyberintelligence is an emerging, constantly evolving field that combines elements of traditional intelligence and information technology to protect digital operations.
It is important to understand that cyber intelligence goes far beyond simply collecting data: it involves transforming that information into valuable intelligence and creating a continuous feedback loop that progressively strengthens defenses.
Phases of cyberintelligence
Understanding the phases of cyber intelligence is fundamental to its rigorous implementation. The process is structured in a structured intelligence cycle, which ensures that the information gathered is converted into actionable decisions:
1. Planning and direction
Every cyber intelligence process begins with defining intelligence requirements: what needs to be known, why, and for whom. This phase identifies the critical assets that must be protected and the most relevant threat vectors for the organization.
2. Compilation
Data is obtained from multiple sources, including open-source intelligence (OSINT), the dark web, the deep web, social networks, specialized forums, vulnerability databases, and threat feeds. Automated cyber intelligence tools allow for continuous, real-time monitoring of these sources.
3. Processing
Raw data is structured, normalized, and filtered to remove noise. By 2026, this phase will have been radically transformed thanks to artificial intelligence, which enables the processing of data volumes that are impossible to manage manually and eliminates false positives that so severely penalize operational efficiency.
4. Analysis
This is the core phase of cyber intelligence. Analysts, supported by AI, interpret processed data to identify patterns, attribute threats, correlate indicators of compromise (IoCs), and anticipate attack vectors. This analysis transforms data into actionable intelligence.
5. Diffusion
The intelligence generated is distributed to stakeholders in the appropriate format, whether through executive reports for management, technical alerts for SOC teams, or threat feeds for SIEM platforms. Cyber intelligence is only valuable if it reaches those who need it at the right time.
6. Feedback
The cycle concludes with an evaluation of the usefulness of the intelligence generated and the adjustment of requirements for the next cycle. This feedback loop ensures the continuous improvement of the cyber intelligence program.
These phases of cyber intelligence form an iterative, non-linear process that must constantly adapt to the evolving threat landscape.
Main Applications of cyber-intelligence
Cyber-intelligence has many practical applications within an organization's cybersecurity strategy.
Brand Protection
Brands, with their reputations, are among an organization's most valuable assets and, therefore, one of the most targeted by cybercrime.
Cyber-intelligence tools currently offer the best strategy for protecting the brand against fraudulent use or abuse.
Control of Third-party risk
In an environment where the IT perimeter has blurred its boundaries in favor of hyperconnection, controlling the risk of the value chain has ceased to be a voluntary protection strategy. It has become an obligation established by the most advanced legislation, such as the European NIS 2 Directive.
These tools allow organizations to control third-party risk using objective, real-time data collected nonintrusively, making third-party permission unnecessary.
Detecting and disabling phishing, fraud, and scam campaigns
Raising awareness among customers, employees, and third parties about phishing, fraud, and scams cannot be an organization's sole strategy for combating them. Organizations must actively protect all these actors, both for safety and for their brand's reputation.
Through Cyber-intelligence, organizations can detect, track, and mitigate phishing, fraud, and scams involving corporate identity theft on social networks.
You may be interested in our post→ Phishing: what it is and how many types there are.
Compliance
Legal systems are becoming stricter regarding organizations' compliance in protecting the personal and sensitive data they handle and controlling the risks posed by third parties.
Cyber-intelligence tools allow not only control over the value chain but also real-time detection of leaks or exposures of an organization's database, as well as the identification of open vulnerabilities that may entail legal sanctions.
Detection and removal of open and exposed vulnerabilities
Open and exposed vulnerabilities on the Internet, the Dark Web, the Deep Web, and Social Networks are within anyone's reach and are exploited by cybercriminals to design attacks.
The longer the vulnerability remains open, the more likely the attack is to succeed. Cyber-intelligence tools enable the organization to detect them almost as soon as they occur.
Locating Leaked Passwords and Credentials
The organization's knowledge of leaked passwords and credentials, along with its real-time location, allows it to change them before they can be used to execute an attack.
Locating Leaked and Exposed Corporate Databases
Cyber-intelligence tools allow the organization to detect any database leak in real time and act quickly to avoid sanctions and damage to corporate reputation.
Protection of intellectual and industrial property
Detecting the unauthorized use of resources on which the organization holds intellectual or industrial property rights is essential to protecting the corporate core's assets.
With cyber-intelligence tools, this fraudulent activity can be detected in real time, and the mechanisms to report and eliminate it can be activated.
Cybersecurity Scoring
The most advanced cyber-intelligence tools allow you to obtain cybersecurity scores for both your organization and third parties, based on objective, up-to-date data.
This capability facilitates decision-making in alliances and collaborations, positioning in contracts with the administration or other agents, and identifying weak points in the cybersecurity strategy.
The Three Types of Cyber-intelligence: Tactical, Strategic, and Technical
Among the different types of Cyber-intelligence, we can find three main ones:
Tactical cyber-intelligence
This type of Cyber-intelligence focuses on immediate threats. It includes identifying specific threat actors, understanding their tactics, techniques, and procedures, and detecting ongoing attacks.
Tactical Cyber-intelligence is essential for incident response and threat mitigation.
Strategic cyber-intelligence
Strategic cyber-intelligence deals with long-term trends and emerging threats. It includes analyzing cybercriminals' tactics, identifying new vulnerabilities, and understanding how the threat landscape will evolve.
Strategic cyber-intelligence is crucial for security planning and decision-making at the organizational level.
Technical cyber-intelligence
Technical cyber-intelligence involves the detailed analysis of technical data related to cyber threats. It includes analyzing malware, identifying indicators of compromise, and understanding how attacks are carried out.
Technical cyber-intelligence is essential for network defense and the protection of digital assets.
Each type of cyber-intelligence plays a crucial role in protecting organizations against threats. Together, they provide a complete view of risks, enabling organizations to protect themselves effectively in the digital environment.
Advantages of using cyber-intelligence at a strategic and tactical level
On a strategic and tactical level, implementing a cyber-intelligence tool offers several advantages to organizations:
- Cyber Threat Prevention: Cyber intelligence enables organizations to identify and mitigate threats before they cause harm. This includes identifying threat actors, understanding their tactics, and detecting vulnerabilities that could be exploited.
- Incident Response: When a security incident occurs, cyber intelligence helps determine what happened, who was responsible, and how to prevent it in the future. This includes actions such as malware analysis, attack attribution, and identification of indicators of compromise.
- Threat Intelligence: Cyber-intelligence provides valuable insights into emerging threats and security trends. It helps organizations stay one step ahead of cybercriminals and adapt their defenses accordingly
- Regulatory compliance: Organizations have compliance requirements, including protecting digital information and susceptible data identified by legal systems. Cyber-intelligence helps organizations comply with these regulations by providing information about the threats and vulnerabilities that must be addressed.
- Digital Investigation: In cases of digital crime, Cyber-intelligence is used to collect evidence and track criminals. This involves identifying the source of an attack, gathering digital evidence, and assisting in the prosecution of criminals.
Discover our cyber intelligence solution for businesses
Kartos, the cyber intelligence platform for businesses developed by Enthec, provides organizations with the most advanced cyber intelligence capabilities on the market.
Kartos obtains, in an automated and continuous manner, real-time alerts and issues reports generated by proprietary artificial intelligence.
An AI so advanced that it enables Kartos to be the only cyber-surveillance platform for businesses capable of eliminating false positives in search results.
If you need more information on how Kartos can protect your business, contact us.
False positives in cybersecurity: How to eliminate them
Imagine a security system that constantly issues alerts, but most of them don't correspond to any real threat. Each alert demands time, attention, and resources, even though in the end there's nothing to address.
In the world of digital security, this phenomenon has a technical name: false positive in cybersecurity.. It is essentially a security alert triggered by legitimate or harmless activity. It seems like a minor problem, almost an anecdote, but for system administrators, it's one of their biggest daily nightmares.
The invisible cost of unnecessary noise
When we talk about a false positive in cybersecurity, we're not just talking about a technical annoyance. We're talking about wasted resources, since security teams have to dedicate part of their time to investigating false positives and alerts that turn out to be false.
This creates two critical problems:
- Alert fatigue. Staff become so accustomed to irrelevant warnings that, when a real threat arrives, they let their guard down. It's the "boy who cried wolf" effect applied to servers.
- Opportunity cost. Every hour an expert spends verifying a false alarm is an hour not spent improving network architecture or searching for real vulnerabilities that an attacker could exploit.
Why do false positives occur?
To eliminate noise, you first need to understand where it comes from. Most traditional security tools operate on a detection scheme based on signatures or patterns.. If anything even remotely resembles suspicious behavior, the system triggers an alert.
Overly rigid configurations
Sometimes, for fear of something slipping through, companies configure their firewalls or intrusion detection systems (IDS) with sensitivity thresholds that are too low. This is like setting a metal detector so sensitive that it beeps even for dental fillings.
Lack of context in the analysis
The software often lacks context. It might detect that an employee accesses the database at 4:00 AM from another country and flag it as a credential theft attack. However, if it doesn't know that the employee is on a business trip in Tokyo, the tool will generate an unnecessary false positive for cybersecurity.
Effective strategies for clearing the threat radar
Completely eliminating the risk of error is impossible, but reducing it to reasonable levels is a matter of using the right methods and technology. Here's how to start filtering out noise:
Refine the detection rules
It is not enough to install a tool and let it work on its own. Cybersecurity requires constant fine-tuning.. It's essential to review alert logs monthly and identify any recurring alerts without a valid reason. If an internal application consistently triggers an alert upon update, a specific exclusion rule should be created.
The role of CTEM (Continuous Threat Exposure Management)
This is where the approach changes. Instead of simply reacting to isolated alerts, many organizations are adopting a more proactive approach the CTEM model.. This paradigm does not only seeks to detect "fires" but to constantly analyze the exposure surface to understand which vulnerabilities are truly critical.
By continuously monitoring exposure, a much clearer picture emerges of what is normal and what is not, drastically reducing false positives in cybersecurity.
Kartos: the solution for companies seeking clarity
In this information-overload scenario, we at Enthec have developed Kartos. . This is not just another tool that adds more noise to a company's cybersecurity management, but a cyber surveillance solution designed with efficiency in mind.
Kartos acts as a platform for continuous threat exposure management for businesses. Its main function is to monitor what happens "outside" your perimeter, on the dark web, in leak forums, or in assets involuntarily exposed.
The key difference is that Kartos doesn't just throw raw data at you. Its artificial intelligence engine filters information so you receive only what truly poses a risk. By providing an external, contextual view of your infrastructure, it minimizes the risk of false positives in cybersecurity, allowing your team to focus on what really matters: protecting the business.
Benefits of integrating intelligent cyber surveillance:
- Automatic prioritization. Identifies which assets are truly at risk.
- Fatigue reduction. Fewer alerts, but more accurate.
- External visibility. Discovers what attackers see about your company before they act.
How to distinguish a false positive from a real threat
For technical teams, establishing a protocol is vital. Not all alerts should be treated with the same urgency. Here's a short guide of steps to follow:
- Verify the source: Does the alert originate from a critical system or a test network?
- Cross-referencing data: Are there other indicators of compromise (IoCs) occurring at the same time? A single event is usually a bug; three related events are usually an attack.
- Analyze behavior: Does the action taken make logical sense within the functions of the user or the affected system?
- Consult external databases: Use threat intelligence sources to verify if that IP or file has been previously reported by other professionals.
The future of detection: AI versus false positives
Paradoxically, the very technology that sometimes generates errors is the one that will help us eliminate them. Artificial intelligence and machine learning are evolving to learn from each company's usage patterns.
You might be interested in > The relevance of artificial intelligence in cybersecurity
An advanced system no longer simply says "this is unusual," but rather: "this is unusual, but it's typical behavior for this server on Monday mornings after a backup." This level of granularity is what will ultimately win the battle against false positives in cybersecurity.
Eliminating false positives in cybersecurity requires a combination of best practices, manual configuration, and, above all, intelligent tools that understand the threat context.. Solutions like the ones we offer at Enthec are designed precisely for that: to give you back the time that noise takes from you.
If you feel your team is overwhelmed by alerts that lead nowhere, or if you're worried about what company information is exposed online, it's time to take the step towards active and strategic monitoring.
Would you like to know how an attacker sees your company? Contact us and discover how continuous exposure management can clear your threat radar today. Don't let the noise prevent you from seeing the real danger.
What is a SIEM system, and how does it work in threat detection?
In a world where cyberattacks have gone from being isolated incidents to everyday occurrences, companies face a major challenge: managing a huge volume of data.
Every time an employee logs in, an email is sent, or a database is accessed, a record is generated. But who's monitoring to ensure all of this is normal? This is where understanding what a SIEM system is and why it has become the brain of security operations becomes crucial.
However, understanding what a SIEM system is is just the starting point. The real competitive advantage comes when your organization takes it a step further and complements that internal detection capability with continuous cyber surveillance of its external exposure surface. Platforms like Kartos automatically monitor your company's digital exposure in real time,so your security team can act before the attacker makes the first move. If you want to identify your organization's exposed vulnerabilities, keep reading.
What is a SIEM system, and why is everyone talking about it?
If we had to explain it simply, a SIEM (Security Information and Event Management) system is a tool that centralizes and analyzes security information from an organization's entire technological infrastructure. It is not limited to a single program; it combines security information management (SIM) with security event management (SEM).
The main objective is to offer a panoramic view.. Imagine you have security cameras, motion sensors, and smoke alarms in a building, but each one works separately.
The SIEM is the control center that receives all those signals, interprets them together, and alerts you if it detects a suspicious pattern.
The evolution towards modern SIEM solutions
Previously, these tools were complex, difficult to configure, and often generated many false positives. However, current SIEM solutions have evolved by integrating artificial intelligence and machine learning.. Now they not only collect data but also learn what "normal behavior" is in your company, so that when something deviates from the norm, the alert is truly useful.
How does the detection process actually work?
To understand the value of a SIEM system, one must analyze its internal workings. It's not magic, but a structured process in several phases:
1. Data collection
The first step is to gather information from all sources: servers, firewalls, antivirus software, cloud applications, and network devices. This data is known as logs or activity records.
2. Normalization and aggregation
Each device speaks a different "language." The SIEM translates all those logs into a common format for comparison. It also groups similar events to prevent the security team from receiving a thousand alerts for the same problem.
3. Correlation of events
This is the critical phase. The system uses predefined rules to connect seemingly unrelated points. For example, if there are three failed password attempts on an accounting server and, one minute later, a database attempts to export an unusually large file to a foreign IP address, the SIEM immediately triggers an alarm.
Examples in the SIEM system: Real-world use cases
To bring these concepts down to earth, let's look at some examples of the SIEM system, which demonstrate their daily usefulness in the IT department:
- Internal threat detection. An employee who typically works from 9 a.m. to 5 p.m. starts downloading confidential files at 3 a.m. on a Sunday. The SIEM detects this anomaly in both timing and data volume.
- Brute force attacks. If hundreds of failed login attempts are detected within a few seconds against an administrator account, the system blocks access and notifies the response team.
- Compliance. Many regulations (such as GDPR and PCI DSS) require keeping records of who accesses what data. SIEM facilitates the generation of automated audit reports.
The missing piece: from reactive detection to continuous management (CTEM)
While a SIEM system is essential, modern cybersecurity is shifting towards a more proactive approach. It's not enough to know what's happening within your walls; you need to know what the attacker knows about you before they press the attack button.
This is where the concept of Continuous Threat Exposure Management comes into play. While SIEM looks inward (at your systems and logs), the CTEM approach looks outward, toward the risk context.
Kartos: Cyber intelligence for businesses
At Enthec, we understand that security is not an isolated field. Our Kartos solution fits precisely within this CTEM framework. Unlike a traditional SIEM that waits to receive error logs, Kartos constantly monitors your company's exposure surface across the web, the Deep Web, and the Dark Web.
If a SIEM system tells you that someone is trying to break in, a tool like Kartos will warn you weeks in advance that your employees' credentials have been leaked on a hacker forum or that one of your suppliers has a critical vulnerability that could affect you.
Why does your company need a holistic approach? Benefits of integrating SIEM with cyber surveillance strategies
- Noise reduction. With a clear view of your external weaknesses and solutions like Kartos, you can configure your SIEM rules to be much more precise.
- Quick response. If you know there is a phishing campaign targeted specifically to your industry (thanks to threat intelligence), your security team will be on alert before the SIEM registers the first malicious click.
- Brand protection. You're not just protecting your servers, you're protecting your reputation. Cyber surveillance helps you detect identity theft and fraudulent domains that attempt to deceive your customers.
The human factor in technology
No matter how advanced any SIEM solution is, the human factor remains the weakest link and, at the same time, the most important.. Technology should serve to empower people, not to overwhelm them with irrelevant data.
That's why at Enthec, we don't just think about organizations; we've also developed Qondar, our solution designed to protect individuals and professionals from digital exposure. Because ultimately, a company's security begins with the security of each and every person within it.
The next step in your security strategy
Understanding what a SIEM system is is the first step toward professionalizing your business's security. It's the tool that will allow you to sleep soundly knowing that there's an "eye" analyzing every unusual movement in your systems. But don't forget that attackers always look for the path of least resistance, and that path is usually outside your internal records.
Combining the analytical power of a SIEM system with the anticipatory capabilities of a CTEM strategy is the only way to stay one step ahead of cybercriminals.
Do you want to know your company's exposure today? At Enthec, we help you see what others don't see. Contact us to discover how Kartos can strengthen your security strategy and continuously reduce your exposure to threats.
8 Tips to Keep Your Email Safe
Email continues to be an essential tool in our daily lives. It allows us to communicate with friends and family and manage important matters related to work or many other aspects of our lives.
By 2026, email security will have taken on a new dimension. Artificial intelligence allows attackers to generate phishing messages that are almost impossible to distinguish from legitimate ones, while the volume of threats grows exponentially. According to the World Economic Forum, Cyberattacks linked to email remain the primary entry point for corporate security breaches globally.
In this article, we explain what email security is, how to tell if an email is secure, and what security measures you should take today to protect your account and your data.
Why is email security critical today?
Email threats have evolved radically. We're no longer just talking about spam or messages with spelling errors: today's attacks are sophisticated, personalized, and, in many cases, almost imperceptible.
The main threats today are:
- IA Phishing (spear phishing generative). Attackers use sophisticated language models to craft phishing emails perfectly tailored to the recipient, mimicking the tone and context of the real company or person.
- Business Email Compromise (BEC). Frauds where the attacker impersonates the CEO, supplier, or business partner to redirect payments or steal confidential information. According to the FBI, BEC losses exceed $2.9 billion annually.
- Ransomware via email. Malicious attachments or links that, when opened, encrypt the device's files and demand a ransom.
- Email spoofing and typosquatting. Falsifying the sender's address or using domains almost identical to the legitimate one to deceive the recipient.
- Multi-layered social engineering attacks. Campaigns that combine email, SMS (smishing), and calls (vishing) to increase the credibility of the fraud.
Understanding the current landscape is the first step in implementing appropriate email security measures.
8 Ways to Make Your Email Safe
From Enthec, we explain 8 ways to make your email safe
1. Choose strong, unique passwords
A strong password is your first line of defense. Although it may seem an essential tip, many people still use easy-to-guess passwords, such as "123456" or "password". To create a strong password:
- Use uppercase and lowercase letters, numbers, and symbols.
- Avoid using personal data such as your birth date or your pet's name.
- Make sure it's at least 12 characters long.
- Consider using a password manager to generate and store passwords securely.
Remember to change your passwords periodically and never reuse the same one on different accounts.
You may be interested in our publication→, How to Manage Passwords and Business Credentials Easily and Securely to Avoid Online Threats.
2. Turn on two-step verification (2FA)
Two-step verification is an email security measure that provides an extra layer of protection. This system requires you to enter a temporary code sent to your phone or generated by an application such as Google Authenticator, in addition to your password.
This method dramatically reduces the risk of someone gaining access to your account, even if they manage to obtain your password. Be sure to enable this option on as many accounts as possible, especially those that contain sensitive information.
3. Beware of suspicious emails
Knowing how to identify a secure email is key to avoiding scams such as phishing, a type of attack in which cybercriminals try to trick you into sharing sensitive information.
If you have any questions about an email that seems suspicious, follow these simple steps:
- Check the sender's address. Attackers often use addresses that mimic those of well-known companies, with slight variations. For example, instead of "support@business.com," it could be "support@bus1ness.com."
- Look at the links. Before you click, hover over the link to check where it takes you. If it doesn't match the official site, be suspicious.
- Look for spelling or grammar errors. Phishing emails often contain errors not found in official messages.
- Don't share sensitive information. No serious entity will email you to ask for your password or banking information.
Don't respond to or click on links in suspicious emails. Instead, contact the sender directly through its official channels.
4. Avoid public Wi-Fi networks to access your email
Connecting to public Wi-Fi networks without security can expose your email to attacks. If you need to use a public connection, consider these options:
- Use a virtual private network (VPN) to encrypt your connection.
- Avoid accessing sensitive information while connected to these networks.
- Turn off the option to automatically connect to Wi-Fi networks.
While convenient, public networks pose a significant risk to your privacy. If you have no alternative, use your mobile data connection to perform essential tasks.
5. Regularly update your devices and apps
Software updates bring new features and fix vulnerabilities that attackers could exploit. Keep up to date:
- The operating system of your computer and phone.
- The email app or client you're using.
- The browsers you use to access your email.
Also, turn on automatic updates whenever possible to make sure you're protected from the latest threats
6. Make regular backups
Even if you take every precaution, there is always a risk that your account will be hacked. Make regular backups of your important emails so you don't lose valuable information; you can use cloud services or save files on a secure external device.
Backups can help you recover your information in the event of an attack and are also helpful if you need to access your data offline.
7. Educate your household members about digital security
If you share devices with others, ensure everyone understands the importance of protecting personal information. Discuss the risks of opening suspicious emails or using weak passwords. Teaching safe practices to your family members can prevent mistakes that compromise everyone's safety.
8. Use advanced protection tools
Today, solutions such as Qondar can help you manage your email security more effectively. These tools detect potential threats and monitor whether your information appears in compromised databases. In this way, in real time, you can detect threats such as compromised passwords for your professional or personal email and the breach that caused the leak, so you can act before cybercriminals use them.
How to tell if an email is safe
Knowing how to identify a safe email is an essential skill. With AI-powered phishing, fraudulent messages no longer have the obvious flaws they once did. Here are the key signs to look out for:
Double-check the sender's address carefully
Don't rely solely on the visible name. Check the real address: attackers use typosquatting techniques (domains with letters changed, added, or replaced). For example, @company.com versus @company-support.com or @bussinness.com.
Check if the email uses TLS
In most email clients (Gmail, Outlook), you can see if a message was received with TLS encryption by clicking on the message details or the padlock next to the sender. An unencrypted email is a sign of risk.
Check SPF, DKIM, and DMARC authentication
In Gmail, you can see the authentication details. Clicking the three dots in the message > "Show original" will help you. If the SPF, DKIM, and DMARC results all show "PASS," the email is likely legitimate. If any of these fail, exercise extreme caution.
Be wary of urgency and unusual requests.
Malicious emails often use a sense of urgency (“Your account will be suspended in 24 hours,” “Urgent payment required”). No legitimate entity will ever ask for passwords, bank details, or urgent transfers via email.
Hover your cursor over the links before clicking
Without clicking, hover your cursor over the link and observe the actual URL in the browser's address bar. If it doesn't match the official domain of the company it claims to be, don't click.
Analyze the attachments with caution.
.exe, .zip, .doc files with macros, or .pdf files may contain malware. If you weren't expecting an attachment from that person, contact them directly through another channel before opening it. If you're unsure, you can upload it to VirusTotal for free analysis.
Qondar: Advanced protection for your emails and personal data
Qondar is a cyber surveillance solution designed for individual users who want to keep their information safe. As a Continuous Threat Exposure Management (CTEM) tool, Qondar allows you to:
- Detect potential vulnerabilities before attackers exploit them.
- Receive alerts on potential security compromises in real-time.
- Monitor the presence of your data in suspicious sources or underground networks.
With Qondar, you can have peace of mind knowing that your email and personal information are protected from digital threats.
Protecting your email security isn't complicated, but it requires consistency and the right tools. From choosing strong passwords to identifying suspicious emails, every step you take shields your privacy.
If you're looking for a complete solution to protect your personal information, Qondar is the ideal tool.
Don't leave your security to chance: start managing your threat exposure with Qondar and always keep your data safe.